CRA Evidence Platform
The compliance platform for EU manufacturers, importers, and distributors. SBOMs, vulnerability workflows, ENISA reporting, and technical files. All in one place.
Your SBOMs, validated and versioned
Drop in a CycloneDX or SPDX file. We validate it against BSI TR-03183 quality criteria, score its completeness, and keep audit-ready records for every product version.
Quality Score
Automatic scoring against BSI TR-03183 standard with improvement recommendations.
Dependency Tree
Visualize direct and transitive dependencies with circular dependency detection.
Version Diff
Compare SBOMs across versions. Track what changed and why.
License Check
Identify problematic license combinations across your components.
Detect new CVEs in minutes, not days
Our Vulnerability Knowledge Base is synced every 15 minutes from NVD/cvelistV5, OSV.dev (aggregating GitHub Advisories, Go, Rust, and PyPI security data), CISA KEV, and EPSS. Our vulnerability scanner runs as an independent verification layer, so a missed detection in one source gets caught by the other. Each finding is enriched with EPSS (Exploit Prediction Scoring System) from FIRST.org to estimate real-world exploitation likelihood in the next 30 days, so you fix what attackers are actually targeting, not just what scores highest on CVSS. Production and staging versions are rescanned automatically, and all findings are cross-referenced with the CISA Known Exploited Vulnerabilities catalog.
What happens when you upload
Traditional Scanners vs. CRA Evidence
| Capability | NVD Only | CRA Evidence |
|---|---|---|
| Coverage | General CVEs | NVD + GitHub + Go + Rust + PyPI |
| Exploit intelligence | CVSS (severity only) | EPSS (real-world probability) |
| CISA KEV alerting | Automatic | |
| Update frequency | Daily | Every 15 minutes (5 sources, local DB) |
| Ecosystem version matching | CPE-based | npm, Maven, Go, Cargo, NuGet, Gem |
| VEX support | Manual export (if any) | Auto-draft from triage → Review → Publish |
Technical Documentation That's Actually CRA-Ready
Article 13 says you need to keep technical documentation for 10 years after placing a product on the market. We generate the Annex VII packages, certificates, and compliance reports so you're not scrambling when a market surveillance authority comes knocking.
Technical File Export
One ZIP with everything: machine-readable manifest (JSON), SBOMs (CycloneDX/SPDX), attestations, compliance checklist, and attribution reports. Human-readable and machine-readable, structured per Annex VII.
EU Declaration of Conformity
Generate EU DoC documents with proper formatting, versioning, and CE marking tracking.
Compliance Reports
PDF or HTML. Vulnerability summary, component inventory, quality scores, and remediation status in one report you can hand to auditors.
Security Data Sheet
Annex II security datasheet wizard. Draft it, validate it, publish it. Export as PDF, Markdown, or HTML.
Certificates
Certificate lifecycle: draft, issue, revoke. Immutable issued certificates with downloadable PDF generation.
Multi-language Documents
Generate documents in 6 languages: English, Spanish, German, French, Italian, Polish.
Annex I Readiness
Score your product against all 20 essential cybersecurity requirements from CRA Annex I Part I. Track what you've met and what's missing.
Artifact Signing
Sigstore-based signing for SBOMs and artifacts. Keyless and key-based modes with signature verification for supply chain integrity.
Support Period Tracking
Define and track the mandatory minimum 5-year support period per CRA Article 13(5). Alerts when products approach end-of-support.
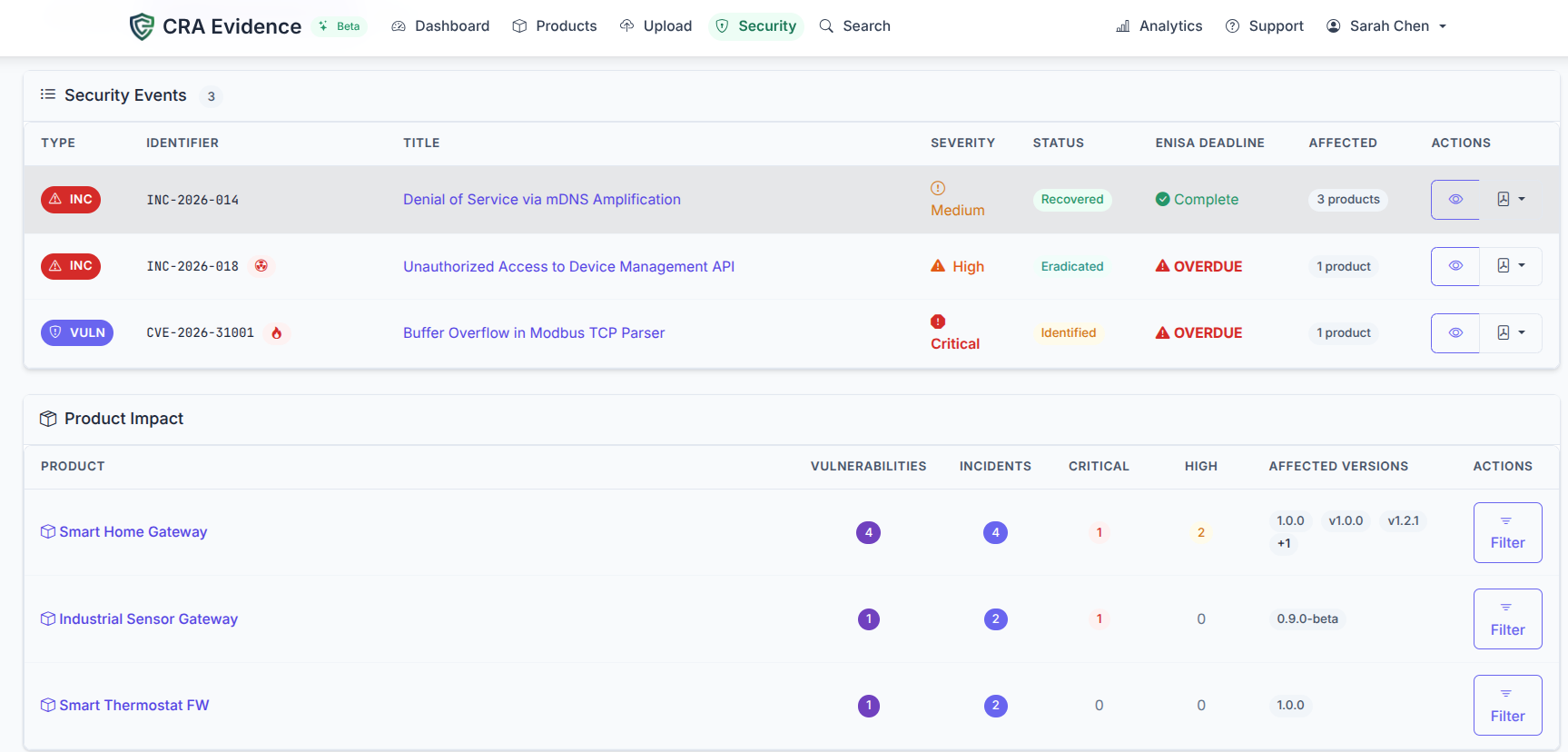
Meet Every ENISA Reporting Deadline
CRA Article 14 requires notifying ENISA of actively exploited vulnerabilities and severe incidents. Two separate tracks with different deadlines. CRA Evidence handles both with structured templates and countdown tracking.
Early Warning
Initial vulnerability notification within 24 hours of discovery. CVE ID, affected products, and attack complexity assessment.
Detailed Notification
Technical analysis with remediation timeline, workarounds, and expanded impact assessment within 72 hours.
Final Report
Resolution confirmation with permanent fix details, deployment timeline, and lessons learned. 14 days for vulnerabilities, 30 days for incidents.
Built for Products With Hardware Components
Machines, embedded systems, and IoT devices need more than software SBOMs. CRA Evidence supports the full hardware product lifecycle.
Manufacturer, Importer & Distributor Dashboards
The CRA puts different obligations on manufacturers (Art. 13), importers (Art. 19), and distributors (Art. 20). Each role gets its own workspace with the workflows that actually matter to them.
Product & Version Management
Products organized by CRA category: Default, Important Class I/Class II, Critical. Each version tracks its release state, environment, and retention tier.
Full Artifact Pipeline
Upload SBOM, HBOM, and VEX per version. Quality scoring and vulnerability scanning kick in automatically.
Vulnerability & Incident Management
CVE tracking, remediation workflows, ENISA notifications. The security dashboard ranks everything by EPSS score and flags CISA KEV entries.
Technical File Generation
Annex VII export packages everything into a ZIP: machine-readable SBOMs, compliance checklists, attribution reports, and conformity declarations. Ready for automated market surveillance audits.
Customer Notifications
Vulnerability notification system for downstream customers. Multi-language templates with distribution list management.
Trust Badges
Embeddable compliance trust badges for your product pages. Link to public verification of your CRA compliance status.
Conformity Assessment Tracking
Track your assessment route based on product category: self-assessment (Default), internal control (Important Class I), or third-party (Important Class II, Critical).
Digital Product Passports
Generate dynamic, publicly accessible Digital Product Passports for each version. QR codes, JSON-LD, and PDF export — multi-language and machine-readable.
Multi-Language Documents
Generate technical documentation, compliance reports, and Digital Product Passports in 6 EU languages: English, Spanish, German, French, Italian, and Polish.
Article 19 Verification Workflow
Step-by-step checklist covering what Article 19 requires: CE marking check, Annex II review, importer ID on product, EU DoC collected, final sign-off.
Manufacturer Registry
Keep track of your manufacturers: contacts, EU representatives, CVD/CSAF metadata. Set how often each one needs reverification.
Stop-Ship Decisions
Found a problem? Block the product. Record your justification, notify stakeholders, and report to the authority. Everything is tracked.
Reverification Triggers
New vulnerability found? Major update released? Review date coming up? You'll get an alert to reverify.
Clone Verifications
Reviewing a new version of the same product? Clone the previous verification. Checklist state and manufacturer data carry over.
Verification Dashboard
See where everything stands at a glance: how many products are verified, pending, blocked, or due for reverification.
Article 20 Due Care Checklist
Everything Article 20 asks for, in a checklist: product ID and traceability, CE marking, EU declaration, manufacturer contacts, anomaly detection.
CE Evidence Upload
Upload your CE marking evidence: photos, scans, certificates. File type and size checks are built in, and everything is audit-logged.
Verification Certificates
Generate PDF certificates proving due care compliance. Includes distributor details, scope, date, and unique verification number.
Stop-Ship Actions
Something's wrong? Stop distribution. The justification is recorded, and authorities and manufacturers are notified.
Portfolio View
See all your verifications in one place. Filter by status, product, or completion date to find what needs attention.
Compliance Progress
Visual progress bars per product. You can see at a glance how far along each verification is and what's left.
Fits into your build pipeline
There's a CLI and a REST API. Upload SBOMs, trigger scans, and gate releases from CI. Works with GitHub Actions, GitLab CI, or anything that can run a shell command.
$ docker run --rm \
-e CRA_EVIDENCE_API_KEY="cra_xxx" \
-v /var/run/docker.sock:/var/run/docker.sock \
craevidence/cli:latest \
upload-sbom \
--product my-app \
--version 2.1.0 \
--image my-app:2.1.0 \
--scan --fail-on high
Upload successful!
Product my-app (created new)
Version 2.1.0 (created new)
Components 142
Quality Score 87%
Vulnerabilities
Critical 0
High 0
Medium 3
Low 1
Works with what you already use
Built to be trusted with your compliance data
Role-Based Access
Owner, Admin, Member, Viewer roles. Scoped API keys with fine-grained permissions.
SSO & MFA
SAML 2.0, Google & Microsoft OAuth, SCIM provisioning. TOTP multi-factor.
Encryption
AES-256 at rest, TLS 1.3 in transit. Argon2id password hashing.
Multi-Tenancy
Complete tenant isolation. Every query enforces organisation boundaries.
Audit Logging
Full traceability of all actions. Queryable audit trail with CSV export.
Rate Limiting
Sliding window rate limiting on login, API, and upload endpoints.
Content Security
Strict CSP headers, CSRF protection, HTML sanitization, and HSTS.
10-Year Retention
Production data retained for 10 years per CRA Article 13. Tier-based retention.
Not sure if the CRA applies to you?
Figure out your obligations before signing up for anything. These tools are free and don't require an account.
CRA Compliance Platform
See it in action: generate your first SBOM in minutes
14-day free trial. No credit card required. Cancel anytime.